Healthcare providers, insurers, colleges, tax accountants… have your crown jewels. They get hacked all the time.
The big data breaches at Yahoo and Target make headlines. In fact, Yahoo’s data breaches, rejuvenated by new disclosures, can’t seem to get out of the headlines. If you use Yahoo with an alias and a fake date of birth, your exposure is limited. If your data is compromised at a retailer, it might include your credit card data, but not normally your date of birth or Social Security number. But if your data is compromised at a healthcare provider, insurer, a university (happened to me), or tax accountant, the hackers gained access to your crown jewels. Those data breaches occur all the time – though they might not make the news.
This year through February 28, according to the Identity Theft Resource Center, there have been 240 data breaches in the US with 1.1 million records “known” as compromised – though the number of records actually compromised is much higher (more in a moment). The ITRC report divides them into five categories. Note the top two:
- Medical/healthcare: 64 breaches, 569,364 records (51.7% of total)
- Business (excl. banking/financial): 120 breaches, 464,540 records (42.2% of total)
- Government/Military: 13 breaches, 39,232 records (3.6% of total)
- Educational: 13 breaches, 39,232 records (2.6% of total)
- Banking/financial: 2 breaches, 0 records “known”
The ITRC defines a data breach as an incident that exposes an individual name plus a Social Security number, driver’s license number, medical record, or financial record (including credit/debit cards) and thus triggers data-breach notification laws.
It also includes incidents that don’t require notification, such as exposure of user names, emails, and passwords without involving sensitive personal identifying information. This number of exposed “records” is not included and shows zero.
The report lists by name the 240 entities where data breaches have been reported so far this year. It also lists the number of records exposed by each entity, though most of the time the number is “unknown” and therefore not included in the totals. So the total number of records exposed is much higher.
Oh, the irony
Here are a few of the entities on that list – some of them ironic, other outright chilling:
- New York Life
- U.S. Anti-Doping Agency
- Cloudflare (which I use to guard WOLF STREET against denial-of-service attacks; they notified me of the breach; there was a “serious bug” in their software and it was “leaking data”; but it was fixed, they said, and they found “no instance of the bug being exploited.”)
- Several CPA and income tax services firms, whose client tax data would surely make them a high-value target
- Boeing
- Klondex Gold & Silver Mining
- Athletic Clubs of America
- Land Title Guarantee Company
- Several investment advisory firms
- Toys “R” Us
- A large number of school districts and public schools
- A large number of universities, including University of North Carolina School of Dentistry, Harvard Computer Society (I mean, really), Georgia Tech…
- Veteran’s Affairs
- New York City Department of Education
- North Carolina Department of Health and Human Services
- Michigan Department of Technology, Management and Budget
- California Correctional Health Care Services
- Alaska Department of Public Safety
- California Department of Justice
- Health insurers, including Highmark Blue Cross Blue Shield of Delaware and Humana (one of the largest health insurers in the US)
- A large number of healthcare providers, including Vanderbilt University Medical Center, West Virginia University Healthcare, St. Joseph’s Hospital and Medical Center (Arizona), Massachusetts General Hospital, Children’s Hospital Los Angeles, Center for Mental Health (Montana)….
- Healthcare services firms, including Medical Information Management Systems
- Walgreen Co.
240 of them, just in the first two months of 2017. Few of the breaches came to the attention of the media.
A new sad record in 2016
In 2016, the number of US data breaches tracked by ITRC soared 40% year-over-year, to an all-time high of 1,093. By the looks of it, this high will be taken out by this summer. The business sector topped the list last year, followed by healthcare:
- Business sector: 494 breaches (45.2% of total)
- Healthcare/medical: 377 breaches (34.5% of total)
- Education: 98 breaches (9% of total)
- Government/military: 72 breaches (6.6% of total)
- Banking/financial: 52 breaches (4.8% of total)
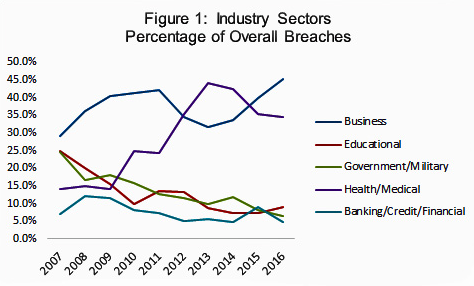
The report provides the chart below. The top two lines: business (blue line) and healthcare (purple line). Clearly, they have not done nearly enough to contain the damage and are more and more targeted. The healthcare sector sits on the most valuable data, including payment-related data such as credit cards, voluminous amounts of health data, date of birth, Social Security number, contact data….
The other categories (government, educational, and banking/finance) are trying to plug the holes more successfully, it seems:
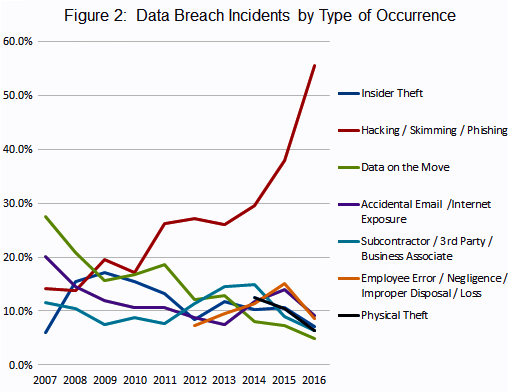
And the chart below shows how “hacking” has become the dominant type of data breach over the years, while the proportion of all other types of data breaches has declined:
In 2016, 52% of the breaches exposed Social Security numbers and 13.1% exposed credit and debit card info. If your Social Security number falls into the wrong hands, you can easily become victim of identity theft.
This is what happened to me, and how I dealt with it:
In 2006, the University of Texas at Austin notified me that “a security breach was discovered in the administrative information system” at the business school where I’d received my MBA years earlier. The information that was downloaded included my name, my date of birth, and my Social Security number. So the crown jewels. And it “strongly” encouraged me “to take precautions” to protect my credit.
Which I did. I did something nasty, something the industry hates: I put a “credit freeze” on my data at the three credit bureaus – Equifax, Transunion, and Experian – after which only financial institutions with which I already did business continue to have access to the data. It blocks all others from gaining access to this data. Hence, it’s nearly impossible for them, or even for me, to open new credit in my name.
This brought a big side benefit: it stopped the avalanche of “pre-approved” credit cards and cash transfer offers in my mailbox, which is a risk on its own. Credit bureaus sell your data to others. That’s their business model. When you put a credit freeze on it, they can no longer sell this data, and they hate it, and they make it as hard and cumbersome as possible for you to do this. But you can do it if you’re relentless enough.
And it has a (minor) drawback, which also shows that this credit freeze works: Even I cannot open a credit account or a deposit account. I can’t get a car loan or a mortgage. In order to get a new credit card, I would have to unfreeze the credit freeze. But I can maintain the financial relationships that I have.
I have had this credit freeze in place since 2006. I think it’s the single best precaution I’ve ever taken to protect myself against identity theft and the worldwide circulation of my credit data. Nothing is 100%, but there are some things we can do to avoid being the low-hanging fruit.
In retail land, more problems: Costs at Costco rose faster than sales, and now its high-flying stock is tanking. Read… Costco Gets Whacked by Inflation
Enjoy reading WOLF STREET and want to support it? You can donate. I appreciate it immensely. Click on the mug to find out how:
![]()


Wolf,
I put a security freeze in place in 2008 after I had an issue with a bogus cc opened up in my name. It took some time but I got my credit reports cleaned up and the bogus info removed. The security freeze has been great as I don’t get hassled anymore.
Does that lifelock really work.
It’s just kind of an insurance (it pays after the fact). It doesn’t protect you against data breaches before they happen.
The best way to secure your finances is to put a freeze at each if the three major credit agencies. They each cost $10. Each time you freeze or unfreeze it is a $10 charge. You don’t need to unfreeze all three when you need more credit, just the agency that is pinged when you apply for credit. This is much cheaper and much more effective than paying for a notification system.
Yes, I did put a credit freeze on all three bureaus in 2006 and have kept it in place, as described at the end of the article. Thanks for the suggestion of just unfreezing the one that gets pinged. One hoop is easier to jump through than three :-)
Wolf, you can ask Experian for a one-time use PIN code that will allow one creditor access to your credit file. It works really well, you don’t have to remove the freeze.
On the rare occasion that I do need to open credit-related accounts these days, I simply shop around until I find a provider that uses Experian. The others, I tell them why I’m moving on.
Transunion has a way to let you lift the freeze just for one specific creditor, but they have to fail to pull your credit file first. The whole process is kinda clumsy but it does work. You call them up, they tell you who has tried and failed to pull you file in the last week, you pick the one that sounds like the people you want to give access too.
Equifax is in the dark ages, they have nothing like any of this.
Thanks. Great info.
I had my data stolen from a healthcare company around 2007. I found out because someone was using a credit card in my name on the ‘net. Fortunately the company they were going through recognized the odd traffic, called me personally, and I stopped the use.
I also put on a credit freeze, though for just one year. Here is the other thing I never thought about. We can do a lot of banking activity with our personal banks on the Internet nowadays. You need to make sure that you go to any accounts you have on the ‘net and set up a password. Before a bad guy does that for you.
Unfortunately most business owners and managers don’t have the requisite skills to manage their network security systems. They don’t even have the skills to hire someone to do it for them. And little thought, if any, is ever given to what actually should and shouldn’t be connected to the Internet. Give out your information very, very carefully and thoughtfully.
Kent,
“We can do a lot of banking activity with our personal banks on the Internet nowadays. You need to make sure that you go to any accounts you have on the ‘net and set up a password.“
If you`re not currently using a password to access your bank accounts over the Internet, then what are you using ?
In the Great Canadian Tradition of blaming everyone else, a large grocery retailer whose customers found that their accounts had been drained of bonus points blamed customers for having weak passwords, as well as hackers breaching other sites and then using the passwords obtained to breach customers’ accounts because many people use the same passwords to access different sites. This stretches the limits of credibility.
They could have just said that their databases had been compromised.
Interestingly, I did have an account with the so-called Equifax Credit Watch protection service, which promised me that suspicious credit card and other activity would be monitored and I would be alerted if such activity took place, ostensibly in real time.
Somehow, crazy charges showed up on my card that I didn’t know about yet (because it wasn’t billing time) and the bank sent me an automatic email, asking me to click on a link to ‘verify’ suspicious charges. Of course I thought it was a phishing scam, and googled the exact text of the email, and sure enough, most people reported it as a scam, so I didn’t do anything else. I got another couple of auto emails, so then got curious and phoned the bank directly and enquired, and was then given a list of bogus charges that I confirmed as fraudulent, which were then reversed.
Still no word from Equifax. After I got my new credit card some time later, I called up Equifax, told them my credit card had been breached and to please change the card number to the new one for the automatic billing. No comment, no alert, no reaction, no query, no interest, nada. they thanked me for correcting my automatic billing information.
Cancelled the account.
Wasted money for zero ‘protection’. I did get a quarterly credit score, which of course you can get for free anyway, and which doesn’t really matter because any monthly bills go straight from the mailbox to payment in about 5 minutes flat.
I only use a new Citicard virtual credit card for any online transaction. You can define a dollar and expiration date for each virtual card generated.
I was attacked by a pleasant enough ransomware thief. I called him up to get my computer unlocked and we chatted while he cleaned his filth out of my files. Of course he wanted my CC # so he could pay himself $100 ( or even more). Sadly for him he tried to send himself a gift certificate from Apple and while it was ‘approved’ initially Apple cancelled it. He tried the same with Amazon and they too cancelled his ‘gift certificate’. He called me back to complain about his problem but I said there was nothing I could do if Apple or Amazon didn’t believe I was buying gift certificates for guys in Pakistan! I cautioned him that I had called Visa and had the card number cancelled so he was just out of luck.
If one uses the internet for any purpose, one should do a full CPU backup periodically.
If you’re hit with a files lockup or intractable infection , Wipe your hard drive and reinstall everything from the backup.
After the installation, and before returning to the internet, erase all cookies and contact any entities where you have had passwords by telephone and arrange to have a temporary password assigned. Then change the password using each entity’s secure webpage, by means of their secure proceedures.
Don’t give the bastards anything but a blank internet address after they contact you.
Super Cookies (LSOs – local shared objects, used with Flash) are a growing, persistent problem. They may be removed using various tools such as BetterPrivacy.
Also, take time to look at bank card activity to see about any unusual activity. That may be relatively innocuous, a simple mistake, or an indicator of something bad. I’ve found that companies are not very fast at processing credits, even to the point of ‘forgetting them’, for example.
Keep a separate list off the computer of all accounts with contact information where you have set up any auto-pay either through credit or debit activity.
Exit your browser routinely, restart, update, take time to manage settings.
As the younger generation says, “Adulting takes more work”.
I found the free program AdwCleaner from Malwarebytes to be effective in getting rid of these malware attacks.
Also – get an IRS pin.
No one can fake file your taxes to get a refund without it.
Thank you, silicon valley.
And thank you, fed govt, for NOT using our social security numbers as ids…
re: “Exit your browser routinely, restart, update, take time to manage settings.”
I do this as well as periodically scan whole computer, all updates, and always logoff at night. I also have the camera disabled.
‘Just because you’re paranoid doesn’t mean they aren’t after you.
Thank you Wolf for this. I just had a medical incident, was required to list all kinds of data that I thought was unnecessary including my SS number.
This was Tuesday and Wednesday in Miami.
Yesterday, I get 6 ‘frantic’ calls from Paypal and texts and emails that something suspicious was going on with my account and to change my password. I logged in on a different computer, and indeed there was the warning, so I changed my password. Paypal even had a follow up call to be sure it was me……impressive protection.
I used the card to make my Co-payment and prescription bill.
Is that not curious?
There are a vast multitude of fishing scams aimed at businesses of all types intent on obtaining identity data. One popular scam is an email to human resources of a business claiming to be someone with authority to obtain employee information such as W-2’s or payroll records. It seems to work regularly. Lots of scams out there that use attached infected PDF’s that when opened go after client identity data. Don’t open a PDF even if purportedly from someone you know unless you verify with the person. Generally don’t open a PDF unless you requested it and you can verify where it came from.
hmm did some sleuthing seems that a credit freeze will not stop prescreened offers of credit per this link. I used the opt out function, which is free, to stop getting these mailings . I think, WR, that the credit freeze still allows the credit reporting agencies to place you on a list that meets certain criteria requested by lets say an insurance company. A credit freeze is the ultimate form of protection though. Only you can look at your report.
https://www.consumer.ftc.gov/articles/0497-credit-freeze-faqs#offers
I only get “preapproved” offers from financial institutions I already have accounts with, or from entities (like my alma mater, grrrr!) that partner with institutions that I have an account with, so for example a university-branded credit card handled by my bank. I think those are the only exceptions.
And the these guys want us to become a cashless society. With so many breeches and pilfering online, you can’t help but ask, what is the REAL reason they want a cashless society?
And the New York Fed got hacked an $100 Million were stolen from the Bangladesh Central Bank.
Awesome, I had no idea one could do this. Do you just call them on the phone to do this?
Google something like: equifax credit freeze … You’ll find the Equifax page with the instructions.
Do this for all three credit bureaus.
Maybe the tools were developed by the CIA in concert with silicon valley, a $100B spying program that left us all vulnerable?