Tech, including Facebook and Google, lent their support to a host of misleading scare tactics.
Wolf here: After the US Congress repealed restrictions earlier this year, your broadband provider (ISPs such as Comcast, Verizon, or AT&T) can monetize your private data. ISPs know practically everything you do on the internet, and they know who you are and have your credit data from credit bureaus such as Equifax. California tried to pass legislation that would have reinstated some of those protections. So this is not just about a legislative defeat of internet privacy in California, but about how lobbyists for the tech industry in general operate.
As this succeeded in California — via falsehoods and national security scaremongering — the campaign is now heading to other state legislatures because the industry wants to monetize all your data in a world where you and your data are the product.
By Ernesto Falcon, Electronic Frontier Foundation.
Across the country, state lawmakers are fighting to restore the Internet privacy rights of their constituents that Congress and the President misguidedly repealed earlier this year. The facts and public opinion are on their side, but the recent battle to pass California’s broadband privacy bill, A.B. 375, suggests that they will face a massive misinformation campaign launched by the telecom lobby and, sadly, joined by major tech companies.
The tech industry lent their support to a host of misleading scare tactics.
Big Telco’s opposition was hardly surprising. It was, after all, their lobbying efforts in Washington D.C. that repealed the privacy obligations they had to their customers. But it’s disappointing that after mostly staying out of the debate, Google and Facebook joined in opposing the restoration of broadband privacy for Californians despite the bill doing nothing about their core business models (the bill was explicitly about restoring ISP privacy rules). Through their proxy the Internet Association, which also represents companies like Airbnb, Amazon, Etsy, Expedia, LinkedIn, Netflix, Twitter, Yelp, and Zynga, among others—Google and Facebook locked arms with AT&T, Verizon, and Comcast to oppose this critical legislation. What is worse, they didn’t just oppose the bill, but lent their support to a host of misleading scare tactics.
How do we know? Because we were on the ground in Sacramento in September to witness every last-minute dirty trick to stop A.B. 375 from moving forward. But there is one positive outcome: ISP and Silicon Valley lobbyists have played their hand. When these tactics are deployed at the last minute by an army of lobbyists, false information is extremely hard to counter by citizens and consumer groups who lack special access to legislators. But over time legislators (and their constituents) learn the truth – and we’ll make sure they will remember it when this legislation comes back around in 2018.
People have not forgotten they had privacy rights that were repealed this year. It is in fact one of the most unpopular moves by this Congress and opposed by voters regardless of political party affiliation. Undoubtedly, the companies and their proxies will recycle what worked in California to other states as legislatures move closer to passing their own bills. To inoculate against misinformation, here is a breakdown of the three most pervasive myths we saw at the final hours.
Let’s not let our lawmakers get fooled again.
Read the Bill: the Definitions Are Rooted in Longstanding Telecom Law
Lobbyists often calculate that some lawmakers are not going to closely read a bill and that these policymakers will instead rely on the word of “industry experts” without checking their claims.
In California, the opposition lobby used this tactic and began claiming that the definition of “Broadband Internet Access Service” (the technical term for an ISP that sells broadband service) was inadequately defined and could burden all kinds of companies that are not ISPs. Technology giants like Google and Facebook, using the Internet Association as their proxy, echoed the false claim, providing the air of legitimacy that added to the intended confusion.
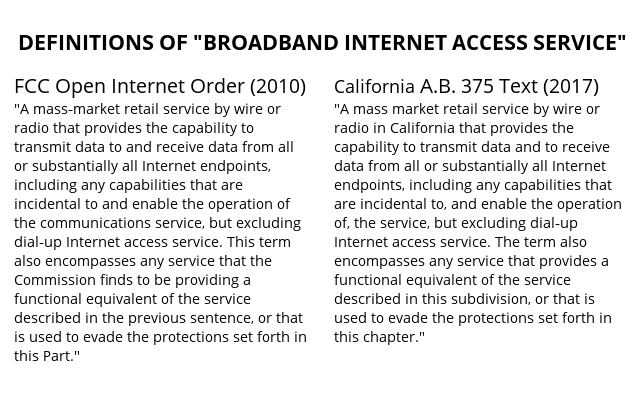
In reality, there was nothing vague or unclear about this definition in A.B. 375. The language in the California bill was copied almost verbatim from the long-standing definition under Federal Communications Commission rules.
You can see for yourself in this side-by-side comparison.
And the bill’s author, Assemblymember Ed Chau, went one step further to explicitly state which entities would not be covered by the bill:
“Broadband Internet access service provider” does not include a premises operator, including a coffee shop, bookstore, airline, private end-user network, or other business that acquires BIAS from a BIAS provider to enable patrons to access the Internet from its respective establishment.
The language couldn’t be clearer. But repeat a false claim enough times from enough paid lobbyists and legislators start to question themselves.
No, Broadband Privacy Protections Don’t Help Terrorists and Nazis
One of the most offensive aspects of the misinformation campaign was the claim that pretending to restore our privacy rights, which have been on the books for communications providers for years, would help extremism.
Here is the excerpt from an anonymous and fact-free document the industry put directly into the hands of state senators to stall the bill:
The bill would bar ISPs from sharing potentially identifiable information with law enforcement in many circumstances. For example, a threat to conduct a terror attack could not be shared (unless it was to protect the ISP, its users, or other ISPs from fraudulent, abusive, or unlawful use of the ISP’s service). AND the bill instructs that all such exceptions are to be construed narrowly.
In addition to national security scaremongering, the industry put out a second document that attempted to play off fears emerging from the recent Charlottesville attack by white supremacists:
This would mean that ISPs who inadvertently learned of a rightwing extremist or other violent threat to the public at large could not share that information with law enforcement without customer approval. Even IP address of bad actor [sic] could not be shared.
There is absolutely nothing true about this statement. A.B. 375 specifically said that an ISP can disclose information without customer approval for any “fraudulent, abusive, or unlawful use of the service.” More importantly, it also included what is often referred to as a “catchall provision” by allowing ISPs to disclose information “as otherwise required or authorized by law.”
The catchall provision is key, since there are already laws on the books allowing services to provide information to the police in emergency situations. For example, the Stored Communications Act spells out the rules under which ISPs are, and are not, allowed to disclose content to law enforcement. The California Electronic Communications Privacy Act (CalECPA), passed in 2015, allows ISPs to disclose information to law enforcement as long as it doesn’t run afoul of state or federal law and allows law enforcement to obtain this information without a warrant in specific emergency situations. Facebook and Google presumably know this, because they supported CalECPA when it was in the legislature. Comcast, AT&T, and Verizon know it too.
The Great, Fake Pop-up Scare
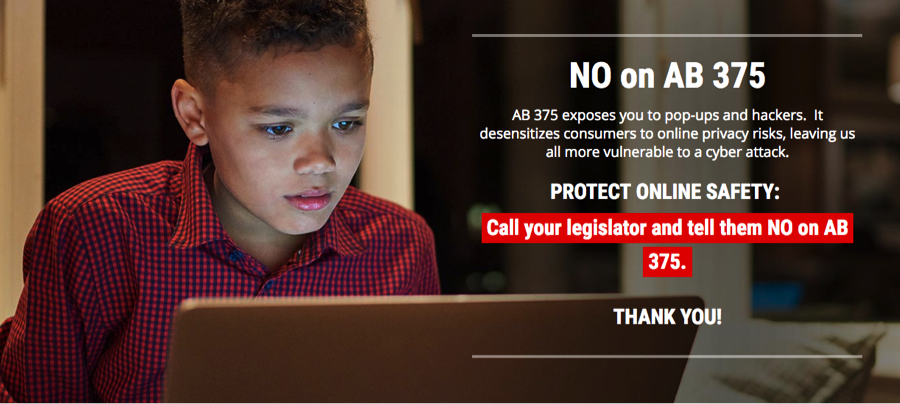
In materials like this advertisement, the opposition lobby claimed that A.B. 375 would result in a deluge of pop-ups that consumers would have to click through, and that in turn this inundation would create a sort of privacy fatigue. Consumers would stop caring, and cybersecurity would suffer.
We’ve debunked most of this tale in a separate post , but let’s address the issue of pop-ups. The bill did require ISPs get your permission (also known as opt-in consent) before monetizing your information that includes the following:
(1) Financial information.
(2) Health information.
(3) Information pertaining to children.
(4) Social security numbers.
(5) Precise geolocation information.
(6) Content of communications.
(7) (A) Internet Web site browsing history, application usage history, and the functional equivalents of either.
But it did not mandate that people have to constantly receive pop ups to obtain that consent. In fact, once you said no, they couldn’t keep asking you over and over again without violating this law and likely laws that regulate fraud and deceptive acts by businesses. However, if the ISP changed the terms of your agreement, they would have to ask your permission again.
Think of it like renting an apartment. If your landlord was going to change your lease agreement, you’d want to know and you’d want to make sure you agreed to any amendments. Being notified of these changes isn’t annoying, it is expected. The only thing that would be annoying is if your landlord kept pestering you to agree to changes you don’t want and did not take no for an answer.
The same applies to ISPs: people are a lot more concerned about ISPs trying to sneak through new invasions of privacy than the alerts they get about those changes.
Internet Users Will Need to Mobilize to Regain our Privacy Rights in 2018
It’s easy to see how lawmakers could be duped in the sleepless, high-speed, waning hours of the legislative session, especially when the information comes from sources that have historically been credible.
In 2018, we plan to make sure that every legislator who was bamboozled by companies like Google, Facebook, Comcast, and AT&T is given the facts. We are confident that lawmakers in states around the nation will continue to push for consumer privacy, filling the gaps created by the Federal Communications Commission as it rolls back network neutrality and privacy protections and AT&T’s efforts in the courts to eliminate the Federal Trade Commission’s authority to oversee telephone companies.
EFF will continue to support state efforts to respond, including dispelling the myths spread by privacy opponents. And we’ll need your help to make sure our legislatures respond to the demands of a vast majority of the public and side with Internet users—not the companies that seek to exploit them. By Ernesto Falcon, Electronic Frontier Foundation.
What else has Equifax not disclosed yet? Read… LEAKED: Worst Data Hack in US History Gets Worse
Enjoy reading WOLF STREET and want to support it? You can donate. I appreciate it immensely. Click on the mug to find out how:
![]()


Nobody was bamboozled they were going to vote that way no matter what.In 2018 no need to inform legislators of the facts just vote them out.But remember this is california they will keep the same clowns in.I’m going to have some more nuts,fruits, and berries.
I agree.
I should care but I know how incompetent most of the ISPs are so it doesn’t bother me much. They are interested in selling bandwidth, if they have to filter everything, their traffic will slow down to a crawl and their customers will leave in droves.
The speed trap is what they don’t understand in government. The more they monitor, the slower it gets, and there is a point where the monitoring overtakes the system.
They can monitor upstream, but not downstream. Usually, there is a huge difference in the bandwidth.
Yup, you said it. California legislature and many municipal governments are corrupt. The state is far too big to be governed effectively.
“Yup, you said it. California legislature and many municipal governments are corrupt. The state is far too big to be governed effectively.”
Should read.
Yup, you said it. California legislature and many municipal governments are corrupt. The state is far too big to be governed effectively. With the multiple flaw, corruption encouraging. American political system, in a modern world.
As I’ve said many times when it comes to the Internet and Telecom’s … free is never free … you have no privacy on the net … nothing is secure in the digital domain … and more importantly .. in their eyes …
You are not the customer .. you are a commodity .. to be bought .. sold .. traded and manipulated in any way possible even to your detriment in order to fill their bank accounts with your hard earned cash .
But as far as us mobilizing ? Against this looney tunes NeoLiberal ( both sides of the aisle ) congress , senate and administration ?
Sorry … Though I’ll give it my best ( and $$$ ) to borrow a quote from Agatha Christie’s mom ;
” I’ll hope for the best but expect the worst because when it comes to expecting the worst… people seldom let you down ”
e.g. The FAANG’s aint about to let go .. unless ….. hmmmm ;-)
Companies are looking for alternate revenue streams. If they had strong organic growth I don’t believe they would pursue this endeavor with such zeal. Everyone one is struggling to keep their piece of a non expanding pie.
“I would have been good, if only I had not had to be bad …”
Erosion of privacy helps Nazi types enormously. To say that enforcing privacy helps them is simply ludicrous. In every country that the Nazis invaded, they went straight for the bureau(s) of statistics. Nobody remembers that American corporate information technology was a critical and major enabler of Nazi efficiency (“IBM and the holocaust” 2001 & 2012). Nobody seems to remember that this is also how communism keeps control of its citizens, and more importantly, the press. Without a free press which can be fed by whistle blowers who have the protection of anonymity (not being tracked by technology), there can be no democracy. However, students are now being trained to spew out all their personal info to some corporate mega cloud. This is a Nazi’s biggest wet dream. If the plethora of (reported and unreported) Equifax style incidents don’t make everyone sit up and take notice about the folly of mega data collection, then the Nazis have indeed won and will ride in on the back of corporate greed. History shows that so called “legal protections” on data use are a joke and can be overturned in a heartbeat. The only way is if the data is not collected in the first place! With an adequate amount of innocuous seeming data, crimes can be retrospectively “fitted” to anyone by some clever A.I. algorithm. This is the big issue: what are they going to do with all the data tomorrow? Meanwhile clueless millenials who have no idea of history are sleepwalking into one of the biggest traps in history and don’t seem to care who knows what about their every bowel movement. Legislators are either corrupt or are mentally deficient and no one seems to care.
BIAS from a BIAS?
Bias: An inclination oftemperament or outlook;especially a personal and sometimes unreasoned judgment, prejudice. A deviation of the expected value of a statistical estimate from the quantity it estimates. “A systematic error introduced into sampling or testing by selecting or encouraging one outcome or answer over others.”
Yes there was a lot of BIAS here alright.
I hate what this country has become.
If you go to an NBA game that uses FlashSeats tickets in Cleveland, Denver, Houston, both LA teams and Minnesota, one person in the group must show an ID; a drivers license or credit card which is electronically read at the admission gate.
In the past, the Timberwolves, for example, had season ticket holders who had accounts with the team. Of course, these accounts were known to the T-Wolves, but season ticket holders could hand off their tickets to other friends to use, and those friends could go to the game anonymously.
Now season ticket holders can transfer tickets only electronically. This is done via email to the friend who has to have a FlashSeats account. The T-Wolves and FlashSeats now have this info. Or a season ticket holder can offer to sell their tickets on the FlashSeats website, and the buyer’s info and price paid is now on both databases. I have been told by an executive that works for the T-Wolves that this data is ‘kept and used’.
In the land of diminished privacy even going to a basketball game puts you “in a world where you and your data are the product.”
The core of FB’s and GOOG’s business models (i.e. the main sources of their profits) is “customer” identifiability, so sellers can more effectively target them. They are the largest media companies in the world for a reason! AT&T, CMCSA and VZ are jumping on the same opportunity. If enacted nationwide, this legislation basically destroys the “customer is the product” business model. No wonder they’re fighting so hard.
… and just to add insult to our injury .. the Washington Post reported today that the FCC has just suffered its first round of deregulation .. to the benefit of the mega broadcasters/corporations .. and to ours and our local stations detriment and ultimately demise .
Free internet? I pay monthly.
Wow thanks for the heads up. That did it. Ad blocking, tracker blocking, Brave, proxies and Virtual Private Networks (VPN) or bust.
But remember: A VPN is only as private as the entity that is providing the VPN. That entity gets to see everything.
“But remember: A VPN is only as private as the entity that is providing the VPN. That entity gets to see everything.”
The only way to deal with this, is to have an “anonymous” mobile connection.
And work very hard at keeping it so.
Which means
1 no identifiable social media.
2 never used Any ID including credit cards on it.
3 Alwasy buy acesse in cash.
Its more expensive but it work’s.
Once you have been the victim of illegal and baseless State communication intrusions You develop a protect a serious privacy shield as a reaction almost naturally.
In the Modern world you can still be smoke, but you have to work at it. It also means at lest 3 individual phone connections.
Since this post is from the EFF, does their Privacy Badger add-on mitigate this situation?
Glancing around at anyone with any amount of power, I am seeing signs of desperation everywhere. This is certainly another piece of desperation. I’m guessing that gradually decreasing energy return on energy investment is offering us all less and less of everything, so anything depending on advertising actually working is going to have problems. It will only get worse for them, and more and more signs of desperation. The analogy of a shrinking pie comes to mind, as well as the one of the cornered tiger.
There are technically a solutions for that problem.
A VPN and some privacy-enhancing measures in the browser help a lot.
The VPN blocks the service provider from blocking and throttling when used with encryption. Then block all JavaScript that is not needed. The next step is to block font reading and then canvas fingerprinting.
With desktop Firefox the noscript extension blocks most tracking scripts and font tracking if @fontface is turned off. Canvas fingerprinting gets blocked as well.
In mobile Firefox those settings can be changed via the about:config page.
If jAvasript is needed, a special extension is needed to block canvas fingerprinting.
Moreover, cookies and history need to be cleared often.
This is not an exhaustive explanation but a starting point to enhance privacy.
Btw, disable flash or get rid of flash cookies aka lso s.
For practical reasons there should be a browser for privacy and another less restrictive for say online shopping with JavaScript enabled to make the shopping work.
The added privacy takes work but I do not know an easier way to get it.
Let me suggest where all this is going, from personal experience.
A while back I bought a piece of equipment from a supplier with an iffy background. They didn’t deliver and I wanted my payment back. By this time I figured they were a bunch of crooks.
They said I could have my refund but they wanted various bits of ID. I’d paid in bitcoin, so all they had to do was refund to the address, no need for ID, or bank details.
It took a while, but I faked the ID details that they wanted.
Now, if there’s one thing that screws up a database, it’s fake information, and that is where all this is going. There’s more, but them’s the basics.